Expert Perspectives from Montra
Montra executives, subject matter experts, and independent authorities provide insights and commentary on the key issues that matter most to you and your business.
Best IT Management Firms in Atlanta: What to Look For
A practical guide to choosing the best IT management company in Atlanta — covering criteria, questions to ask, pricing benchmarks, and what good looks like.
Montra Wins 2025 Future of Work Award for Via Workforce Manager
Montra’s Via Workforce Manager recognized for advancing the modern workplace through employee-first innovation in identity lifecycle management.
Montra Achieves SOC 2 Type II Compliance
Independent auditor confirms the operating effectiveness of Montra’s security and confidentiality controls
Identity Lifecycle Management for Fast-Growing Tech Companies: Challenges and How to Solve Them
Identity Lifecycle Management (ILM) plays a crucial role in improving security, compliance, and operational efficiency. Read about the challenges and keys to success for companies implementing ILM.
The Evolution of IT Asset Management Software in 2024: Converge the Data
As IT asset management continues to evolve, it increasingly intersects with adjacent domains such as device monitoring, device security, and inventory management. We examine here the latest trends shaping asset management software in 2024, examining notable advancements, emerging features, and evolving end-to-end processes.
Device Protection 101: Safeguarding Businesses through Effective Device Monitoring
Businesses are increasingly reliant on technology to optimize business operations and stay competitive. Let’s delve into the top 5 ways monitoring devices can elevate your business’s protection levels and empower your workforce, especially ensuring uptime, availability, security, and compliance.
Four Ways to Revamp IT Rollout Efficiency for Retail
Retailers, in their effort to modernize, encounter a formidable challenge. Implementing new technology across numerous stores has unique configuration requirements.
Three Obstacles to Better IT Onboarding and How to Avoid Them
Discover how embracing advanced IT onboarding solutions can mitigate common onboarding challenges, paving the way for seamless integration of new employees into the workforce.
What Is Identity Lifecycle Management? A Practical Guide for Modern IT Teams
In today’s digital landscape, where data breaches and cyber threats are prevalent, businesses are increasingly focusing on Identity Lifecycle Management (ILM) to safeguard their sensitive information and ensure secure access control. ILM is the process of managing user rights to systems, applications and data, over time as their roles evolve in an organization.
Send Them on Their Way: The Benefits of Automating Your IT Offboarding Process
Saying goodbye can be tough, especially when it comes to offboarding employees. There’s paperwork to collect, access to revoke, and a multitude of other tasks to complete. And, let’s be honest, no one wants to waste their time on a process that’s notorious for being bureaucratic and time-consuming.
Four Reasons to Outsource IT Logistics and What to Look for in a Partner
IT logistics is the set of process a business must execute to securely and efficiently deploy and manage IT devices in their operations.
Montra Included in Atlanta Inno 2023 Fire Awards
Montra has been identified by Atlanta Inno as one of 25 Atlanta companies as an honoree in their 2023 Fire Awards. The Atlanta Inno team considered factors such as funding, revenue growth, mission and future potential when selecting the finalists.
Identifying and Stopping Phishing Attempts: 5 Tactics
We go over five tactics to identify and stop phishing – a common tactic for cybercriminals to gain access to your organization’s sensitive data.
Laughing at Hackers: 5 Proactive Steps You Can Take to Secure Your Laptops from External Threats
Here’s a joke that’s not funny: your company’s data was just hacked. Shock waves, unmitigated panic, and alibis are all fair play when you as the CIO, CISO or Head of IT, wakes up to the news that a hacker has infiltrated their systems.
Montra Continues Growth and Moves Up the 2023 Inc. 5000
Montra ranks No. 1,399 on the 2023 Inc. 5000, its annual list of the fastest-growing private companies in America and is among the top 200 software companies in the United States.
The Basics of Unified Communications as a Service: A Crash Course for Business Leaders
As a business leader, you know that communication is key to success. In this post, we’ll give you a crash course on the basics of UCaaS, so you can determine if it’s the right fit for your organization.
Why a Cybersecurity Compliance Program is Necessary for Every Business
As a leader, you are responsible for ensuring that your organization’s data remains secure and protected from cyber threats. Cyber-attacks can result in the loss of millions of dollars, loss of customer trust, and reputational damage from which it can take years to recover.
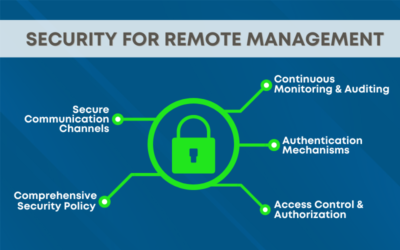
Remote Management System Deployment: Beware of the Security Risks
Remote management systems have evolved into a valuable tool for IT professionals, enabling remote access, monitoring, and management of their organization’s IT infrastructure. However, as with any technology, they come with inherent risks.
How Hybrid Work is Affecting Remote IT Management: A Crash Course
As the world continues to adapt to the changing landscape of work, the concept of hybrid work has emerged as a popular model for many organizations. Hybrid work combines elements of remote work and in-person collaboration, allowing employees to have flexibility while also maintaining some level of face-to-face interaction.
Montra Releases Notable Updates To Its IT Management Platform
Today, Montra announces updates to its award-winning platform, providing customers with improved navigation and an increased breadth of available features.
Leveraging Technology to Enhance IT Onboarding
Employee onboarding is a crucial process for any organization, and it’s especially important for the IT department. However, onboarding is often a lengthy and complex process, and without the proper tools and resources, it can be difficult to get new hires up to speed quickly.
Montra Expands Customer Base with Addition of Discovery Storage
Montra announces today it has signed Discovery Storage as a new customer, handling the company’s distributed IT management needs.
Mastering IT Logistics Management: 5 Things Retailers’ IT Asset Tracking System Should Deliver
Read this article from Retail Info Systems about Mastering IT Logistics Management: 5 Things Retailers’ IT Asset Tracking System Should Deliver
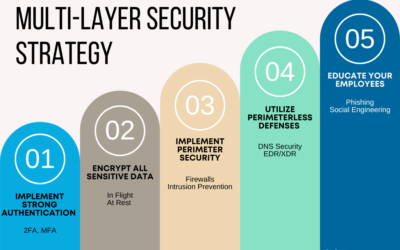
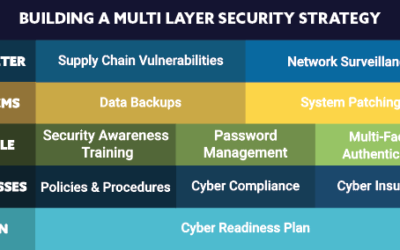
Cyber-readiness Strategy 12: Multi-Layer Security Strategy
Security is asymmetrical. Where businesses must plan, prepare and defend against every threat or scenario, cybercriminals only need to find a single weakness or hole in your defenses to carry out their malicious plans. Protect your data and your business by deploying multiple security strategies together as one.
Montra Makes the 2022 Inc. 5000 in First Year of Eligibility
Inc. has revealed that Montra, innovator of advanced remote IT management solutions for today’s workplace, is No. 1,976 on its annual Inc. 5000 list, the most prestigious ranking of the fastest-growing private companies in America.
Cyber-readiness Strategy 11: Reduce Supply Chain Vulnerabilities
Cybersecurity threats to the global supply chain can come from anywhere in the world, and they can have a devastating impact on businesses of all sizes. Increased digitization of the supply chain makes it all the more vulnerable.
Montra Ranked on Channel Futures 2022 MSP 501
Montra Ranked on Channel Futures 2022 MSP 501—Tech Industry’s Most Prestigious List of Managed Service Providers Worldwide
Benefits of Microsoft 365 and Azure Active Directory for Identity Management
Microsoft 365 and Azure Active Directory together provide centralized identity management, single sign-on, and enhanced security — and Montra’s Via platform makes them easier to manage.
The Top 5 Benefits of Azure Active Directory
Azure Active Directory provides single sign-on, multi-factor authentication, centralized user management, and scalable identity security for businesses of any size.
Laptop Security Best Practices
Essential laptop security best practices for businesses — covering physical security, strong passwords, EDR software, and safe online behavior to protect company data.
Cyber-readiness Strategies 9 and 10: Passwords and Insurance
Two critical cyber readiness strategies for businesses: combating weak passwords with strong password policies and managers, and protecting your organization with cyber insurance.
Three Tips to Improve HR and IT Process Integration
Three practical tips to improve HR and IT integration for employee onboarding and offboarding — including communication, automation, and the right software tools.
Policies Management in Microsoft 365
A guide to Microsoft 365 policy management — covering security and compliance, WiFi, data loss prevention, and web policies, with best practices for IT administrators.
Checklist for IT Employee Offboarding
A nine-step IT employee offboarding checklist to protect your company’s network, data, and systems when an employee leaves — with a free downloadable infographic.
7 Step Checklist for Secure and Reliable Laptop Imaging
Your company’s laptops are a valuable business tool that enables the success of your workforce. It contains important information and files that are necessary for your work. That's why it's...
TAG Announces the Top 40 Innovative Technology Companies in Georgia
Media Contact: Russ Davis – russ@tagonline.org (404) 920-2023 TAG Announces the Top 40 Innovative Technology Companies in Georgia ATLANTA (April 13, 2022) – Each year, the Technology Association of...
12 Cyber Readiness Strategies #7 and #8
Cyber readiness strategies 7 and 8: how continuous network monitoring and employee security awareness training protect your business from cyberattacks and phishing.
Building a Multi-Layer Security Strategy Infographic
Download Montra’s multi-layer cybersecurity strategy infographic — covering 12 privacy and security frameworks to help your business defend against cyber threats.
Six Steps to Successful Employee Offboarding
Six essential steps for secure employee offboarding — disabling accounts, collecting devices, erasing data, notifying vendors, and maintaining cyber compliance.
Microsoft OneDrive – Eight Ways to Get the Most from It
Eight tips to get the most from Microsoft OneDrive — covering mobile and desktop use, file syncing across devices, collaboration, version history, and offline access.