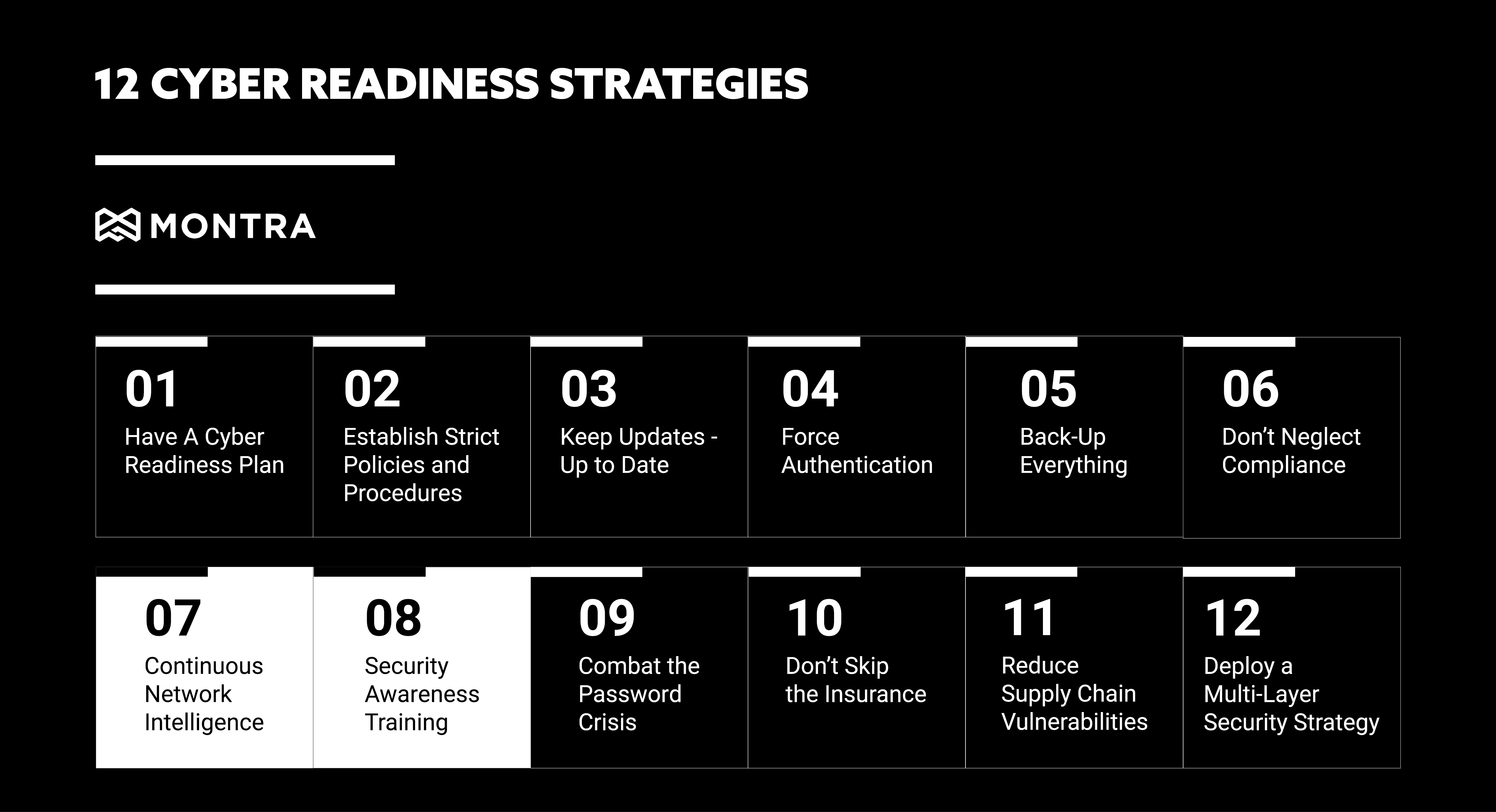
In our last blog post, we discussed cyber readiness strategies: #5 Back-Up Everything and #6 Don’t Neglect Compliance. Continuing our series this week are discussing strategies #7 and #8, Continuous Network Intelligence and Security Awareness Training. In 2021 businesses suffered 50% More Cyberattack Attempts per Week in 2021 and as a business owner, it is not only important to continuously monitor your networks for any suspicious activity, but also to prepare employees for any type of cyber attack.
7. Continuous Network Intelligence
Technology is always changing and advancing, which can mean new vulnerabilities for your organization. Staying on top of these changes is critical to reducing the risk of a cyberattack. This is where continuous network intelligence comes in. By monitoring your network and systems continuously, you can quickly identify and patch any vulnerabilities. In fact, continuous monitoring is one of the best ways to detect a cyber-attack early. One of the strategies attackers will use is ransomware attacks. What is a ransomware attack? A ransomware attack is when an attacker encrypts your data and demands a ransom to decrypt it. These attacks can be devastating to businesses, as they can lose critical data and be forced to pay a ransom. To prevent these attacks, it is important to set up your network to detect access from outside sources. As soon as anyone outside your network enters, you will be able to kick them out before they can cause harm. If you don’t have monitoring tools in place already there are a few ways to start implementing continuous network monitoring:
- Use a network security solution that provides real-time visibility into your network traffic and activity.
- Keep systems up-to-date by continually watching for OS and application security updates and patching the systems as soon as reasonable.
- Conduct regular penetration testing to identify any weaknesses in your system.
By continuously monitoring your network, you can quickly identify and patch any vulnerabilities. This will help reduce the risk of a cyber-attack and keep your business running smoothly.
8. Security Awareness Training
In addition to continuously monitoring your networks, it is also important to prepare employees for any type of cyber attack. This is where security awareness training comes in. Around 91% of breaches started with a phishing attack and 81% of cyber-attacks are related to stolen or weak passwords. By educating employees on the latest cybersecurity threats and how to prevent them, you can reduce the risk of a successful attack. There are a few things to keep in mind when creating a security awareness training program.
- Make it mandatory for all employees.
- Keep it up-to-date with the latest threats.
- Test employees regularly to ensure they are understanding the material. Examples of this include:
- Computer-based awareness training
- Phishing simulation exercises
- Awareness campaigns
- In-person security awareness training
- Monthly notifications or newsletters
By following these tips, you can create a security awareness training program that will help keep your business safe. And by educating employees on the latest cybersecurity threats and how to prevent them, you can reduce the risk of a successful attack.
These are just a few of the many precautions that should be taken to protect your business from a cyberattack. If you would like more information or have any questions, contact Montra at sales@montra.io.



