Montra Achieves SOC 2 Type II Compliance
Montra Technologies Achieves
SOC 2 Type II Compliance
Independent auditor confirms the operating effectiveness of Montra’s security and confidentiality controls
ATLANTA, GEORGIA — (September 2, 2025) — Montra® Technologies today announces the successful completion of its SOC 2 Type II examination. This achievement reinforces the company’s commitment to security, confidentiality, and operational excellence for its customers.
Laika Compliance LLC conducted the independent audit. The firm evaluated the design and operating effectiveness of Montra’s controls over a six-month period, from February 1, 2025 to July 31, 2025. The examination covered the Trust Services Criteria for Security and Confidentiality, as established by the American Institute of Certified Public Accountants (AICPA).
The auditor found that Montra’s software and services description was fairly presented. Moreover, the controls operated effectively throughout the review period. As a result, the audit confirmed reasonable assurance that Montra met its service commitments and system requirements.
“This achievement reflects the discipline and rigor we bring to both our managed IT services and the Montra Via Platform,” said Matthew Singley, COO of Montra Technologies. “Our customers trust us with their data, systems, and users — which is mission-critical to their businesses. Achieving SOC 2 Type II demonstrates that our security controls are not just designed well, but that they operate effectively over time.”
What SOC 2 Type II Means for Customers
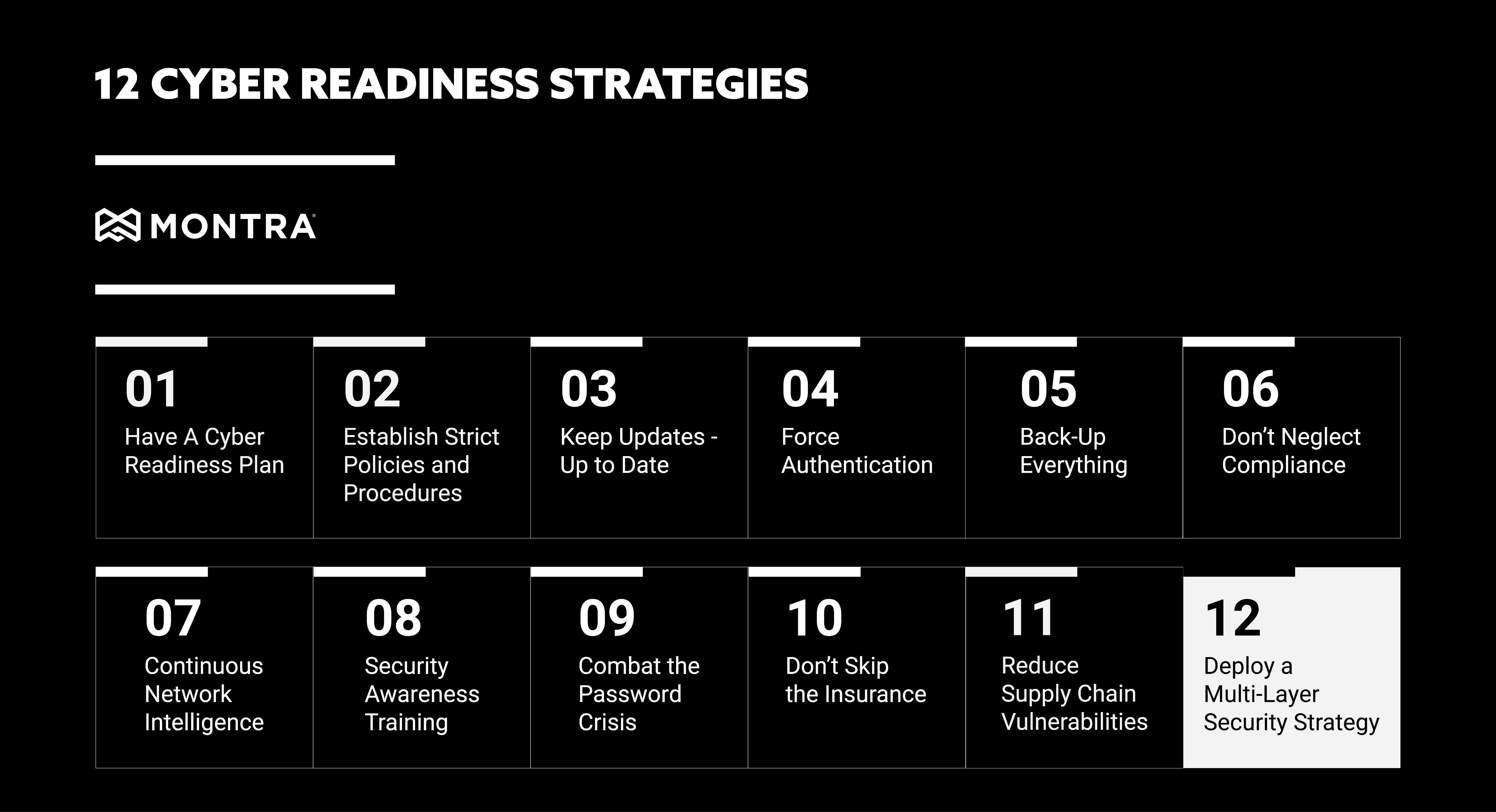
SOC 2 Type II compliance shows that Montra has implemented and maintained effective controls across key operational domains, including:
- Logical and role-based access controls
- Change management and secure software development
- Vulnerability management and patching
- Continuous monitoring and incident response
- Data classification, retention, and secure disposal
- Vendor risk management and oversight
Notably, the audit confirmed no exceptions across tested controls during the review period.
Montra delivers its services across multiple platforms and infrastructure layers. Furthermore, the company incorporates layered security measures including encryption in transit and at rest, multi-factor authentication for privileged access, network segmentation, intrusion detection, and continuous vulnerability scanning.
Strengthening Trust in Unified Identity and Device Lifecycle Management
This SOC 2 Type II compliance covers the Montra Via Platform. Via supports critical IT operations such as onboarding and offboarding automation, device lifecycle management, SaaS access management, security monitoring, and logistics orchestration.
Via is the company’s unified identity and device lifecycle management (UIDLM) platform. It brings together identity, device, application, and logistics data into a single system built for modern, distributed workforces.
By embedding security controls directly into identity and device workflows, Montra helps mid-market organizations reduce operational risk. Additionally, this approach minimizes human error and supports alignment with Zero Trust security principles.
“For many growing organizations, onboarding, offboarding, and device management are where operational risk quietly accumulates,” Singley added. “Consequently, SOC 2 Type II reinforces that our platform is built on a foundation of structured governance, strong internal controls, and continuous risk management.”
Ongoing Commitment to Security and Compliance
SOC 2 Type II is part of Montra’s broader commitment to industry-standard safeguards. These safeguards span administrative, technical, operational, and organizational controls, including HIPAA compliance.
In addition, Montra conducts annual risk assessments, quarterly vulnerability scans, and ongoing monitoring. Together, these practices ensure the company’s security posture evolves alongside emerging threats.
The SOC 2 Type II report is available to customers and prospective customers under NDA.
About Montra Technologies
Montra Technologies is a managed IT services and solutions company. The company delivers secure, scalable technology operations for modern organizations. From identity and access management to device lifecycle management, SaaS governance, security, and compliance, Montra simplifies IT so businesses can focus on growth.
Montra combines decades of enterprise IT expertise with modern, intelligent automation. As a result, the company reduces risk, improves security, and enhances the technology experience across modern workforces. Learn more at www.montra.io and follow us on LinkedIn and X.
Media Contact:
Monty Rachleff
Marketing Manager
Montra Technologies
+1-404-665-9675
mrack@montra.io