Is your business ready to handle a targeted cyber-attack? Maybe you have been attacked and don’t even know it. According to the the 2020 Thales Data Threat Report, 49% of US companies have already experienced a data breach. To help you become more proactive and effective at defending against cyber threats, we are discussing 12 Cyber Readiness Strategies over the next few blogs.
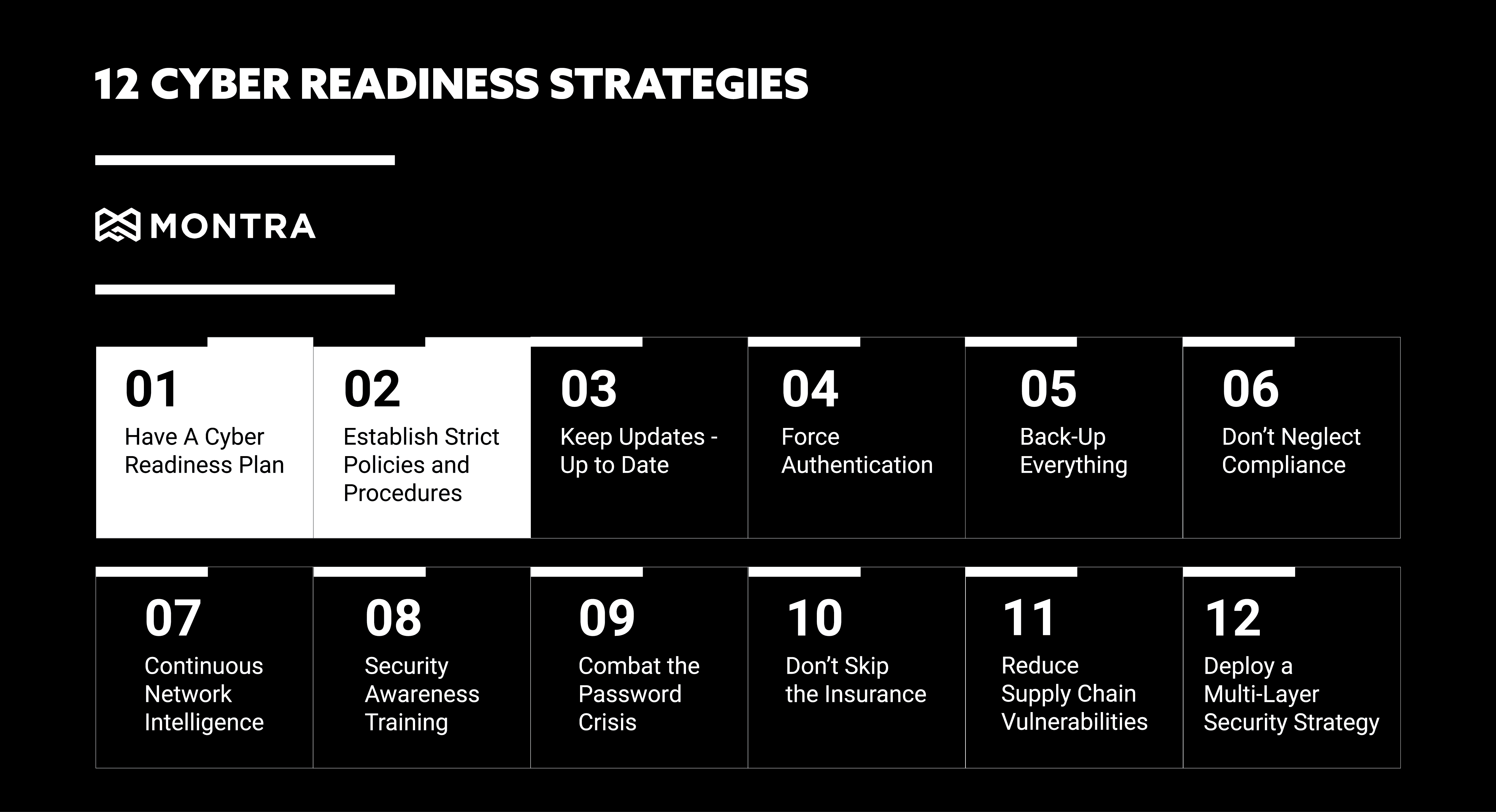
1. Have a Cyber Readiness Plan
It may seem obvious, but to properly address all of the cyber-security threats to your organization, you first need to have a plan – specifically a Cyber Readiness Plan. Your ability to quickly and cost-effectively overcome security threats or breaches determines your business’s success and survival. How you handle and protect your data is central to your business’s security and customers, employees, and partners’ privacy expectations. You need a cyber readiness plan that includes prevention, continuity, and recovery strategies. The Federal Communications Commission provides an excellent planning guide that identifies six critical areas of cybersecurity for companies to address:
1. Privacy and Data Security
2. Scams and Fraud
3. Network Security
4. Email
5. Website Security
6. Mobile Devices
Download the associated cheat sheet as an easy outline to understand each of these areas to help you quickly navigate these best practices and assess your readiness.
2. Establish Strict Policies and Procedures
Cybersecurity policies and procedures help guide secure business operations and are essential for defining the standards of business conduct, system controls, employee awareness, and workplace definitions and expectations. While establishing strict, security-focused protocols is crucial, a system of validation and enforcement is equally important. In fact, all major cybersecurity and privacy frameworks, such as NIST CSF, ISO 27001, HIPAA, and PCI DSS, all require periodic auditing or continuous monitoring to make certain that policies are properly put into operation.
To help you start building your cybersecurity policy and procedure library, we have provided a few policy templates to start. Click to download 12 IT policy templates that are critical to any IT operation.



