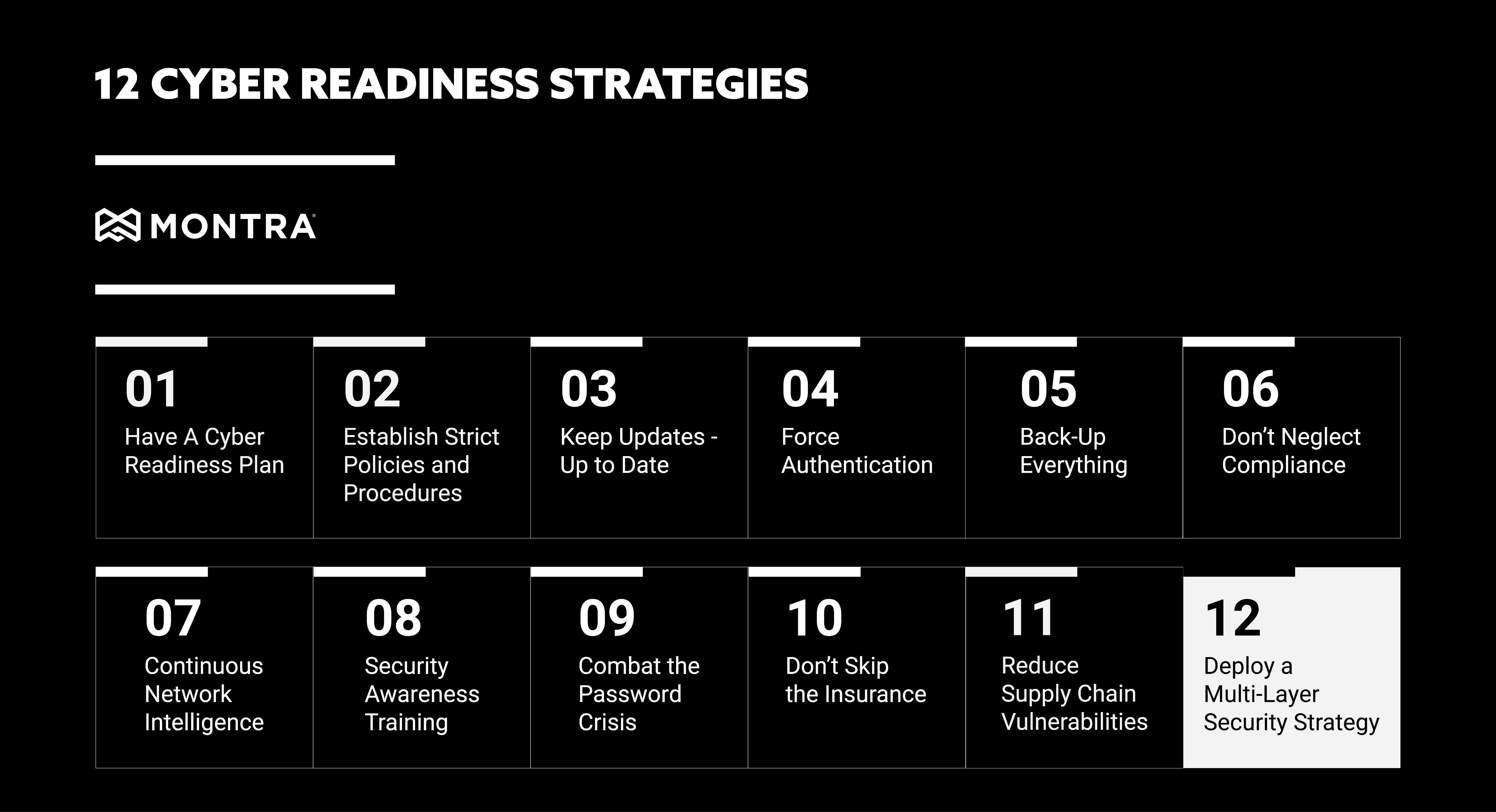
Cyber-readiness Strategy 12: Multi-Layer Security Strategy
Security is asymmetrical. Where businesses must plan, prepare and defend against every threat or scenario, cybercriminals only need to find a single weakness or hole in your defenses to carry out their malicious plans.
Protect your data and your business by deploying multiple security strategies together as one. By using a multi-layer security approach, you can make it much more difficult for cybercriminals to penetrate your organization and cause serious damage.
When it comes to cybersecurity, businesses cannot afford to take chances. Deploying a multi-layer security strategy is the best way to protect your data and your business from the ever-growing threat of cybercrime.
A multi-layer security approach uses multiple security measures to create a defense in depth. By using multiple layers of security, you can make it much more difficult for cybercriminals to penetrate your organization and cause serious damage.
Here are 5 tips for building an effective multi-layer security strategy:
1. Implement Strong Authentication Measures
One of the most important components of a multi-layer security strategy is strong authentication. Authentication is the process of verifying that someone is who they claim to be. There are many different authentication methods, but the most common are something you know (like a password), something you have (like a security token), or something you are (biometrics).
Using multiple authentication factors – known as two-factor (2FA) or multifactor authentication (MFA) – is the best way to ensure that only authorized users can access your data. Requiring MFA makes it much more difficult for cybercriminals to gain access to your systems, as they would need to have possession of all the required factors.
2. Encrypt All Sensitive Data
Another important element of a multi-layer security strategy is encryption. Encryption is the process of transforming readable data into an unreadable format. Encrypting sensitive data helps to protect it from being accessed by unauthorized individuals, even if they can penetrate your defenses.
Encryption should be implemented for data “at rest” and “in flight”. Most web services today will use secure socket layer (SSL) encryption to encrypt communication sessions “in flight” between users and the service. Data sitting on a storage device – hard drive or SSD – is “at rest” and can most often be encrypted using features the device operating system (OS). It usually needs to be activated during setup and a policy control needs to be set so it cannot be turned off.
3. Implement Perimeter Security
Your workforce and company resources in your offices need to be protected by sophistication perimeter security techniques. A firewall controls the flow of traffic between your private network and the public Internet. It can be used to allow or block traffic based on a set of rules. This helps to protect your network from unauthorized access and malicious activity.
Intrusion detection and prevention systems (IDPS) are another important layer of security. These systems are designed to detect and prevent unauthorized access to computer networks. IDPS can be deployed as hardware, software, or a combination of both. They work by monitoring network traffic and looking for suspicious activity that may indicate an attempted intrusion. When IDPS detect suspicious activity, they can take action to block the attempt and alert the system administrator. This helps to prevent attacks before they can do any damage.
4. Utilize Perimeterless Defense Systems
When your workforce is working outside the office, they are also outside the firewall. When this is the case, other “zero-trust” or “perimeterless” tactics need to be added. If the user’s device OS supports a firewall, it should be activated and managed by policies that can be pushed from a central authority. DNS Security – both DNS filtering and DNS encryption should be implemented to prevent users being redirected to fraudulent sites without their knowledge.
Finally, endpoint detect & respond (EDR) software should be installed on any user device to help prevent malware, ransomware or other malicious code from infecting the device.
5. Educate Your Employees
One of the most important components of a company security strategy is education. It is essential that all employees are aware of the risks associated with cybersecurity and the best practices for avoiding them. Employees should be trained on how to identify phishing emails, spot social engineering attacks, and understand the importance of keeping their passwords safe.
In addition, employees should know what to do if they suspect that their account has been compromised. They should know how to report suspicious activity and whom to contact for help. By educating your employees about cybersecurity risks and best practices, you can help to protect your business from attacks.
A multi-layer security strategy is the best way to protect your business from cybercrime. By implementing multiple security measures, you can make it much harder for cybercriminals to succeed in their attacks.
By following these tips, you can make it much harder for cybercriminals to succeed in their attacks. Implementing a multi-layer security strategy is an essential part of protecting your business from the ever-growing threat of cybercrime. By doing so, you can help to ensure that your business is as safe as possible from the ever-growing threat of cybercrime.
So what are you waiting for? Implement a multi-layer security strategy today to help keep your business safe from cybercrime. If you would like more information or have questions about how strong your cyber-readiness is, please contact Montra at sales@montra.io.